Local Active Directory Implementation -2
Step 20:- Once you log in to the admin account. Click on Start and then go to Administrative Tools. Then click on Active Directory Users and Computers.

Step 21:- Click on cyberdetector.com and then on click on Users.

Step 22:- Here Right Click on any blank space and then scroll to New and then click on User.

Step 23:- Here it will ask for the details of user/employee you want and I created a user Vaibhav here. Click on Next after filling the details of the user.

Step 24:- I missed one photo which asks “ do you want the user to change the password on the first login” an “should his password expires after some time or never expires.” I choose the user cannot change password and password never expires. Then click on Finish button.

Step 25:- Type gpedit.msc or just go to Group Policy Management in administrative tools.

Step 26:- Here select the forest (cyberdetector.com in my case) in which select the domain which I keep the name same of the forest(you can change if you want)

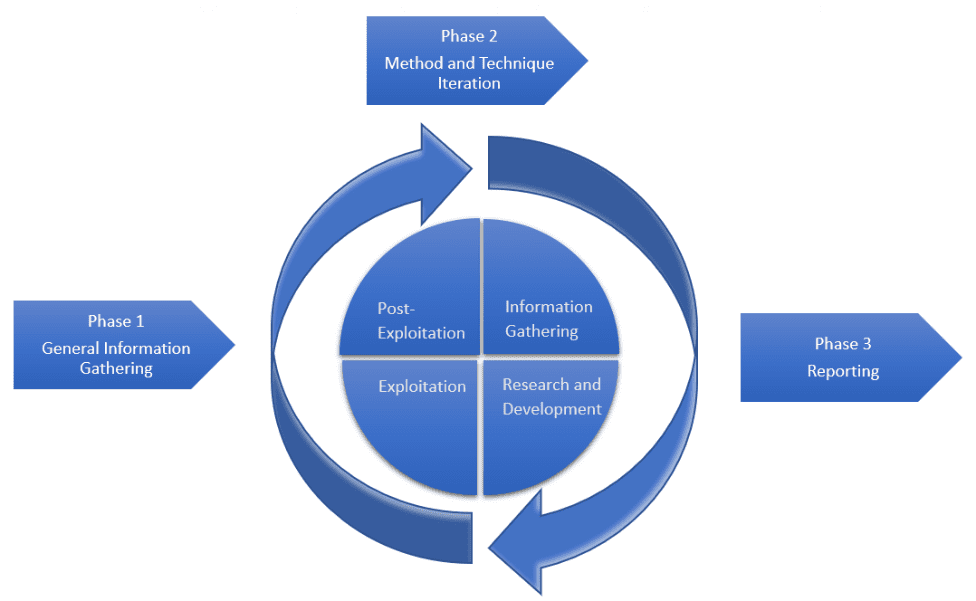
Step 27:- Here we are going to create a new group policy which is one of the mottoes of this active directory. Right-click on domain name and click on “Create a GPO in this domain, and Link it here…”.

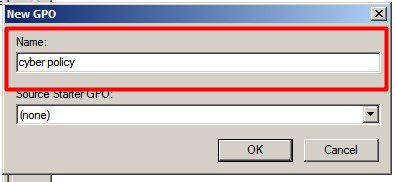
Step 28:- Now give a name to the policy. I gave the policy name as cyber policy. Click on Ok. Then click on Edit

Step 29:- Here you will find two things Policies and Preferences. Policies are the rules which we want to apply for the user account. Policies are like forceful things which are necessary. Preferences are the recommendations which if are there then it will be well and good and if not available then there will be no issues.

Step 30:- A new window will appear on screen here we want a policy for users, so go to User Configurations then Policies. Here we can apply different policies according to our need. I am showing you an example here by restricting the control panel for the user. Go to Administrative Template and then select control panel to do so.

Step 31:- Select “Prohibit access to the Control Panel” then right-click on it and click on Edit.

Step 32:- Select Enabled to enable this policy. Then click on OK.

Step 33:- Now we have to add users to whom these policies should be applied. To do so select on policy and click on Add button.

Step 34:- Provide the name of the user/users we want to add to this policy.

Step 35:- Remove all other Authenticated Users so that this policy should not be applied to other users.

Step 36:- In User PC go to Network and Internet Settings and then click on Existing Network i.e. Local Area Connection.(make sure server and user are on the same network)

Step 37:- Click on Properties. Then IPv4 Properties.


Step 38:- In IPv4 setting properties change the DNS as the IP address of the Server we had set up earlier.

Step 39:- Go to System Properties and click on change settings.

Step 40:- In System properties change the domain by clicking on the change button. Now select the domain and write the domain name you have created. In our case it is cyberdetector.com


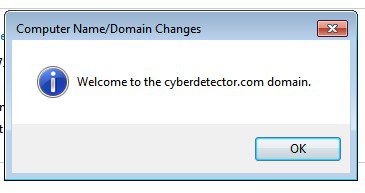
Step 41:- Fill the domain administrator details here and then click on OK button. Then a message will pop-up which welcomes us to the domain. Click on Ok.

Step 42:- Now the system will restart. After that, it will ask to log in and by default for the first time the first the login screen will be of old credentials. Click on Switch User. Then click on Other User.


Step 43:- Now fill the user/employee credentials and login into the account using Enter or the button provided.

Step 44:- After logging into the user account then search Control Panel then try to open it.

Step 45:- An error message will pop-up restricting us to open the Control Panel. Which shows us that the policies are successfully applied. Which was our main target of this tutorial.

That’s all about this blog. Join CertCube labs for career-oriented training and certifications.

Recent Comments