Decrypting IOS apps Essentials
Frida way:-
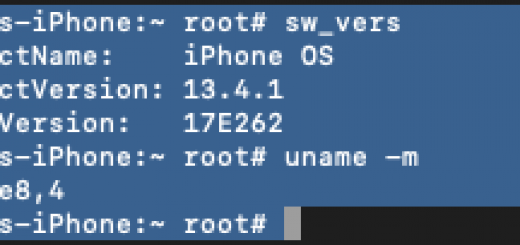
Step 1: Install Frida on the system (Mac/Windows) and iPhone
I’m using my Linux pentesting box and installed Frida using #pip install Frida-tools
Step 2: install the Frida on the jailbroken iPhone. Add Cydia repo build.frida.re and install Frida.
Step 3: Once Frida is installed on the pentest machine and iPhone, perform a smoke test using #frida-ps -U
step 4 : Connect to iPhone (over USB) and select the app you want to decrypt
Download Frida dump iOS from https://github.com/AloneMonkey/frida-ios-dump.
After connecting iPhone over USB, use iproxy / without proxy for SSH over USB
In dump.py, make sure the ip and port is configured
Step 5:You can list the apps (to be decrypted) using #python dump.py -l
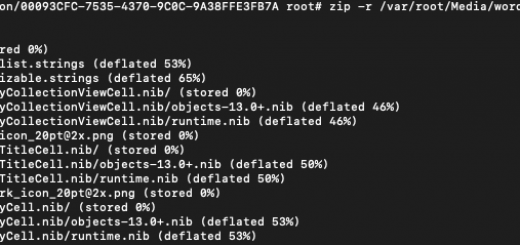
Step 6 : you can use any app for decryption #python dump.py com.bla.bla
Step 7 : Here you go !! you have decrypted ipa !!!
BFINJECT WAY:-
Once you’re jailbroken, you are ready to start penetration testing. Generally, the first step is to crack your chosen target app and inspect its files and binary. you will do this using a tool called ‘bfinject’.
Bfinject is a .dylib injection tool for iOS. It includes both decryption functionality, and cycript (which we will get to later).
To install bfinject, start by downloading the tarball here. Then you will need to copy it over onto your device:
- In your terminal that is ssh’d into your phone, to create a folder by typing:
$ mkdir bfinject - Then, you will need to transfer the tarball onto your device and into the bfinject folder. You can do this in a lot of ways – You can use SCP, but I prefer to use Cyberduck, which you can download here. If you’re using CyberDuck, go to ‘Open Connection’ at the top left, choose SSH protocol, and log in using the same IP/password as before (you can leave the port as 22).
- Now, in either Cyberduck or by the terminal, navigate into the bfinject folder on your device, and upload the tarball from your Mac. To do this in Cyberduck, click on ‘Action’, and then ‘Upload’.
- Finally, run:
$ tar xvf bfinject.tar
Before you run bfinject, you will need to download ‘Core Utilities’ from Cydia. Open up Cydia and search for it. Once you’ve selected it, go to ‘Modify’ and then ‘Install’.
Now we are ready to crack your first app. This can be most any app downloaded from the app store (that you have permission to test!). Make sure the app is open and in the foreground on your phone, and that your phone is plugged into your computer. In your root terminal, navigate to the bfinject folder and run:
$ bash bfinject -P <AppName> -L decryptAfter a few seconds, you should get a message on your phone that the decryption is complete. You can say ‘No’ when it asks if you’d like to use Netcat. Now, to get the decrypted .ipa file, you need to find the app’s directory on your phone.
In Cyberduck or Terminal, navigate here: /private/var/mobile/Containers/Data/Application
As a note – since the directories in your phone can be kind of confusing, to get to the ‘var’ directory, you will need to ‘cd ..’ from ‘root’, which is where you initially are after ssh’ing in.
Inside the Application directory, you will see a bunch of folders with random names. Each of these corresponds to an app on your device. To help you quickly figure out which one corresponds to your target app, you can sort on Cyberduck by ‘Modified’, and the most recently installed app should be the first. Go inside that folder once you’ve found it, and inside its Documents directory, you will find the decrypted-app.ipa. Download it in Cyberduck by going to ‘Action’->’Download as’. Rename the file as whatever you want, but make sure to change the extension to ‘.zip’ instead of ‘.ipa’ so you can easily inspect the contents.
Now you have officially decrypted and downloaded your first app!
CLASS-DUMP WAY :-
The next tool we are going to use is extremely valuable – it will dump the runtime headers of the app’s classes and will help us to understand the app’s structure, and to choose where we want to target.
To install on your Mac, open up a new terminal and run:
$ brew install class-dumpThen, find the app’s executable. After you unzip the .ipa/.zip file you copied to your computer, you will find it in the resulting folder at the path /Payload/AppName.app/AppName
Now, you can run
./class-dump <AppName>.app/AppName > DumpedIf you get an error, you can try installing a different spinoff of class-dump: try this or this. Depending on the version, if you still get an error try changing <AppName>.app/AppName to just <AppName> or <AppName.app>.
Now, open up the ‘Dumped’ file in your favorite text editor, and you should see all of the app’s runtime headers.
Recent Comments